What is cyber security within the finance industry?
Maintaining trust in financial services is business-critical for both attracting and retaining clients. It is essential to implement measures to preserve the confidentiality of client data within your advice technology and ensure internal governance is at the forefront of every licensee and advice business.
There is an expectation on financial institutions is to protect consumer data and privacy across their products and services, with regulators imposing an integrated cyber risk strategy to further enhance their safeguard.
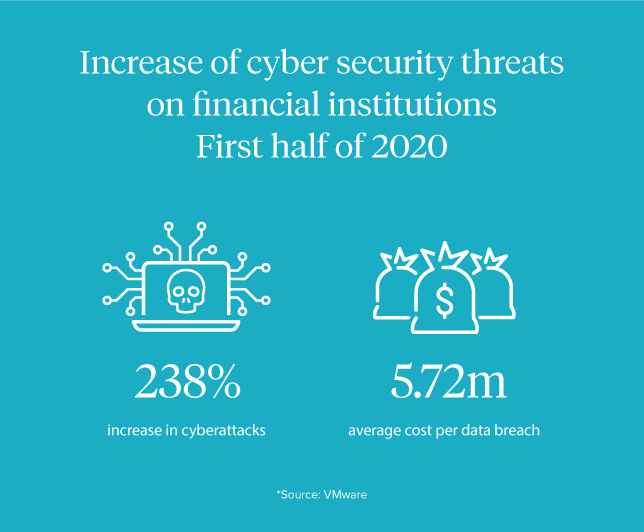
Cyber security threats on financial institutions are increasing - according to VMware, the first half of 2020 saw a 238% increase in cyberattacks on financial institutions. This saw an average cost of $5.72 million per data breach.
With these statistics in mind, there is a significant chance that your advice business will one day encounter a cyberattack. Proactive action and adequate preparation to combat these threats are critical, though do require a solid strategy and regular governance.
ASIC took a stance regarding cyber security following the recent proceedings against RI Advice. The position was unexpected from the perspective of the licensee community, as they did not anticipate the prosecution committing the AFS Licensee holder liable for the cyber attack, therefore exposing the risk and responsibility for the wider industry.
As the cyber security space is constantly shifting, knowledge is power when it comes to protecting your business from security breaches.
So, what are the most common types of cyber attacks on the finance industry?
Here is a list to help you understand the types of cyber attacks:
Malware
Malware is downloadable software, which can be sent via an email with a link disguised as a software update or other fake web page, intended to trick the user into engaging. It’s designed to infect the user’s computer and manipulate how it functions. It also may spy on them or destroy their data. Malware is very easily spread from computer to computer. Though firewalls can detect malware, people must also be educated to pay attention to potential malicious links or attachments before clicking on them.
Phishing
Phishing is a type of social engineering that takes effect by ‘fishing’ or ‘baiting' users through an appearance of legitimacy to divulge sensitive information or login details, to ultimately gain access to systems. Most commonly, phishing occurs via email, SMS, or through a generic link to a fake web page that extracts login information once the user is engaged. These links can also contain malware, which is then used to embed a virus or gain unauthorised access.
In the first half of 2021, phishing attacks within the financial services industry increased by 22%, and financial application attacks saw an increase of 38% in the same period.
Historically speaking, the finance industry tends to be the most targeted sector of phishing attacks, with the Akamai report claiming that 50% of all phishing attacks are on financial businesses.

Brute-force attack
As the name suggests, brute-force attacks occur when the attacker guesses a user’s system login details, and once discovered, they force their way in. These attacks often use automated bots to identify users' credentials, as it can otherwise be a time-consuming exercise.
As the name suggests, brute-force attacks occur when the attacker guesses a user’s system login details, and once discovered, they force their way in. These attacks often use automated bots to identify users' credentials, as it can otherwise be a time-consuming exercise.
On average, a hacker spends three to six months monitoring emails, intending to intercept and systematically use brute-force attempts to uncover system passwords.
To prevent these attacks, lock-out policies should be maintained within the system’s security architecture. These measures help to identify a user’s IP address when logging in to the relevant software and lock out users after a certain number of attempts so they cannot bypass it.
Web Attacks
Web attacks usually refer to vulnerabilities in web-based applications, like online banking. The user may be fooled by a fake web page, a pop-up, or a script to ask to change their login details. Following this interaction, the hacker can obtain those details and login as if they were the user. If it were a banking application, they can then withdraw and send money to another bank account.
Web attacks usually refer to vulnerabilities in web-based applications, like online banking. The user may be fooled by a fake web page, a pop-up, or a script to ask to change their login details. Following this interaction, the hacker can obtain those details and login as if they were the user. If it were a banking application, they can then withdraw and send money to another bank account.
Ransomware
Ransomware is another type of cyber security attack, where cybercriminals can lock a user out of their system via malware. Typically, this access to private information is utilised to hold the user ransom for extortion.
Bank Drops
Cybercriminals obscure their location and use stolen client information to open fake bank accounts by means of stolen personal credentials like date of birth, driver's license information, or other account details. This is also referred to as full data and is often sold on the dark web or the black market.
Why is cybersecurity vital for a financial licensee or adviser
The world of cyber security is ever-changing, and cyber risk is no longer simply a technology issue. In fact, cybersecurity measures need to start with an organisation’s people, to facilitate awareness, activities, and training, and create a culture that instills cyber as a serious issue.
Following the recent RI ruling, the precedent has now been set for our industry, and a licensee is liable for any cyber breaches for any practice or Authorised Representative licensed under their AFSL.
It’s estimated that 93% of advice businesses do not have the appropriate cyber policies and procedures, so it is critical that licensees and practices work together to take the necessary measures to enhance cyber.
In order to preserve a firm’s brand, maintain shareholder value, and characterise trust, a successful cyber security strategy requires a collaborative approach, especially between a licensee and practices. There are a few key principles financial firms engage with when approaching cyber security, including risk & governance, intelligence & agile, and resilience & recovery.
Penalties of cyber breaches for your organisation
The following laws in Australia pertain to cybersecurity:
- Privacy Act (Cth)
- Crimes Act 1914 (Cth)
- Security of Critical Infrastructure Act 2018 (Cth)
- Criminal Code Act 1995 (Cth)
- Telecommunications (Interception and Access) Act 1979 (Cth)
The decision handed down in the Australian Securities and Investments Commission v RI Advice Group Pty Ltd [2022] FAC 496 case on 5 May 2022 found RI Advice failed to act efficiently and fairly, and failed to have adequate risk management systems, calling attention to the need for action, and to the heightened role of cyber security within the industry.
The implications highlighted by this case see that AFS Licensees are exposed to risk where cyber security is not adequately managed across all touchpoints, extending through to the network of authorised representatives licensed within the group.
The field of cyber now adds to the innumerable compliance obligations of an AFS holder. Consequently, this also highlights some key issues that require immediate attention and action:
-
licensees can enforce cyber risk management controls and standards as a condition of authorisation to authorised representatives,
-
cybersecurity exposure must be actively managed with the assistance of cyber experts,
-
the financial penalties & legal costs in the failure to adequately manage cyber risk exposure and breach are significant,
-
the strengthening of indemnities for potential losses arising as a result of cyber incidents, and;
-
the rights to conduct external cyber security audits
Steps and measures to enhance your cyber practices
Whilst there is no silver bullet to the perplexities of cyber security, and considering that it is impossible to eliminate the risk of breaches entirely, there are, however, ways to effectively manage your cyber defenses.
A successful cyber security risk management protocol must be a strategic one, engaging with the below principles:
- Risk & governance: well-constructed policies, procedures, and risk awareness across the licensee and AR network
- Intelligent & agile: timely threat identification, agile ability to adapt and respond through intelligent and critical decision-making
- Resilience & recovery: the ability to plan, anticipate, stand up to and recover from compromises with minimal disruption
In many instances, cyber-attacks recycle the same attack sequence as there are common security vulnerabilities across the array of financial entities in the licensee network.
The implementation of the following security controls could address most of the exposures facilitating data breaches in the financial services sector:
-
Third-Party Risk Management (TPRM) - A third-party risk management program will identify security vulnerabilities for all third-party cloud services to prevent supply chain attacks.
- Multi-Factor Authentication - An MFA policy will make it very difficult for threat actors to compromise privileged credentials.
- Firewall - A regularly updated firewall is capable of detecting and blocking malware injection attempts.
- Attack Surface Management - An attack surface management solution capable of detecting data leaks will significantly reduce the chances of a successful data breach, both internally and throughout the vendor network.
- Learn TTP (Tactics, Techniques, & Procedures) - Threat actors often use similar attack strategies due to similar vulnerabilities across the industry.
In addition, some good cybersecurity measures for licensee and advice businesses alike include:
- Have clear contractual terms, policies & governance between Licensee and ARs across information security, data storage, cybersecurity, fraud procedures, password policies, and privacy,
- Employ credible third-party cybersecurity expertise to conduct regular reviews and audits on governance, policies, and systems, as well as consult on breaches,
- Deploy endpoint device protection across staff,
- Ensuring computer systems have up-to-date antivirus software installed and operating,
- Engaging with the appropriate level of cybersecurity, IT & data management insurance & indemnity cover across the group,
- Use firewalls for emails and backup systems,
- Update password practices ie: sharing passwords between staff and use of default passwords,
- Deploy cyber training and professional development across the AR network,
- Use incident reporting where cyber incidents are notified and escalated,
- Password-protect client documents containing personal information sent via email,
- Utilise MFA/2FA on all software systems,
- Ensure your AdviceTech covers cybersecurity with adequate governance, policies & indemnities,
- Use a client portal with 2FA/MFA to interact with clients over email (adds a layer of extra security over email), and;
- Ensure all staff is trained adequately on cyber (ie: social engineering).
In need of an all-in-one solution to protect your business from cyber threats?
We trust The Cyber Collective, and Cyber Indemnity Solutions to help you protect your clients and secure your business.



